Identity and Access Management (IAM) is often approached from a tools perspective i.e. Azure AD, Okta, or other platforms. But in reality, strong IAM starts with structure, access design, and lifecycle management.
In this case study, I designed a complete IAM model for a fictional fintech company, WiboCore Bank, focusing on:
- Organizational structure
- Access control (RBAC + SoD)
- Joiner, Mover, Leaver (JML) lifecycle
The goal was to simulate a real-world IAM environment that reflects the challenges of securing financial systems.
About WiboCore Bank
WiboCore Bank is a digital-only fintech operating in Kenya and the UK, offering mobile-first banking services.
Key IAM Risks:
- Insider fraud in finance operations
- Overprivileged engineering access
- Delayed deprovisioning of users
- Weak governance over privileged accounts
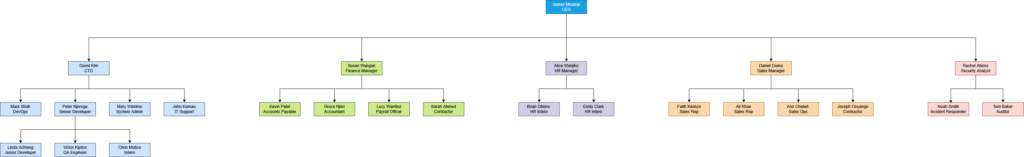
Organizational Structure (IAM-Driven Design)
The organizational structure was designed to support secure access control and approval workflows.
- Each employee has a direct manager – enables approval-based access.
- Departments are clearly separated – enforces Separation of Duties (SoD).
- Security operates independently – ensures audit integrity.
Key Departments:
- Engineering & IT
- Finance
- Human Resources
- Sales
- Security (independent function)
Access Control Matrix (RBAC + Least Privilege)
Access at WiboCore Bank is governed by:
- Least Privilege
- Role-Based Access Control (RBAC)
- Separation of Duties (SoD)
Example Access Design:
- Developers:
- GitHub – Write
- Finance System – No Access
- Finance Team:
- Accounts Payable – Write (no approvals)
- Finance Manager – Admin
- Security:
- Read-only across all systems
Access Control Table
You can view the full Access Control Table from the WiboCore Bank Access Control Matrix document.
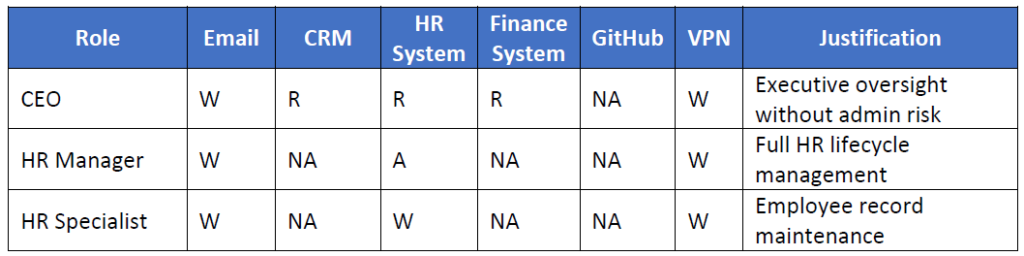
Key Security Decisions
- CEO access downgraded to reduce risk exposure.
- System Admin restricted from Finance systems.
- Developers cannot deploy to production.
- Finance roles strictly separated to prevent fraud.
Joiner, Mover, Leaver (JML) Process
IAM at WiboCore is driven by the HR system as the source of truth.
🟢 Joiner (Onboarding)
Trigger: New employee added in HR system
Process:
- Account automatically created
- Access assigned based on role
- MFA enforced
- Manager approval for elevated access
🟡 Mover (Role Change)
Trigger: Role or department change
Process:
- Old access removed
- New role-based access assigned
- Approval required for privileged roles
Key Control:
👉 No access accumulation
🔴 Leaver (Offboarding)
Trigger: Employee termination
Process:
- Account disabled immediately
- Sessions terminated
- Access revoked across all systems
SLA:
👉 De-provisioning within 5 minutes
Governance and Security Controls
To strengthen IAM, WiboCore enforces:
- Multi-Factor Authentication (MFA) for all users
- Just-in-Time (JIT) access for privileged roles
- Quarterly access reviews
- Full audit logging
- Separation of Duties across critical systems
Key IAM Design Principles
This project was guided by:
- Least Privilege – Users only get what they need
- Separation of Duties – Prevent fraud and abuse
- Centralized Identity Source – HR-driven lifecycle
- Approval-Based Access Control – Manager accountability
Key Takeaways
Designing IAM is not just about tools, it’s about:
- Structuring organizations correctly
- Defining access clearly
- Automating lifecycle processes
This case study demonstrates how IAM can be designed from the ground up for a fintech environment, balancing security, usability, and compliance.
You can view the following documents for more details: